A2A Protocol: Deep Dive
Views: 0

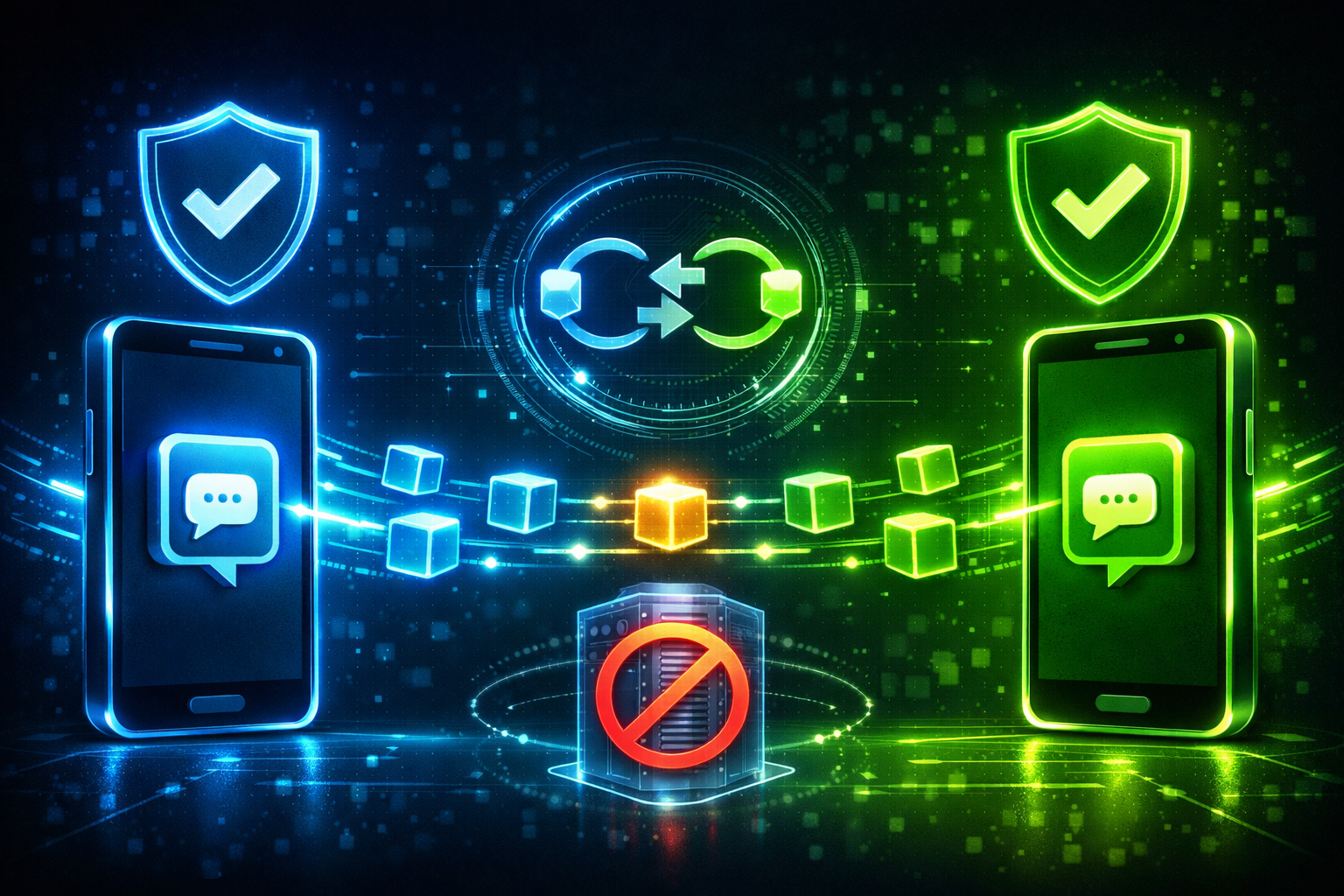
In today’s increasingly decentralized world, applications need to communicate with each other directly — securely, efficiently, and without relying on centralized intermediaries. This is where the A2A protocol comes into play.
A2A stands for App-to-App communication. It’s a protocol that enables one application (like a crypto wallet) to interact directly with another (like a decentralized app or service), securely exchanging data, verifying actions, and initiating processes — all without forcing the user to jump through technical hoops.
Why does this matter?
Think of it like this: you’re using an app on your phone to send money. Instead of copying wallet addresses, scanning QR codes, or confirming three different pop-ups, the apps just “talk to each other” behind the scenes and complete the task securely. That’s A2A in action.
In this post, we’ll explore what the A2A protocol is, how it works, where it’s used, and why it’s shaping the future of decentralized interaction.
What is the A2A Protocol?
The A2A Protocol is a method that allows one application to interact directly with another in a secure, verifiable way. It’s commonly used in the Web3 ecosystem, especially for wallet-to-dApp interactions, but the concept is applicable far beyond crypto.
The goal of A2A is to eliminate friction. Rather than relying on users to act as middlemen — copying and pasting addresses, manually signing messages, or switching between tabs — applications can securely send requests and receive responses directly, often using the user’s mobile wallet or secure identity.
Think of A2A as the digital equivalent of two apps shaking hands, agreeing on what needs to be done, and then executing it — without bothering you unless absolutely necessary.
The Real-Life Analogy: Bob Goes to the Bank
Let’s make it simple.
Imagine Bob wants to send money to his friend Alice. He gets in his car and drives to the bank. At the bank, he tells the teller, “Please transfer $500 to Alice.” The teller checks Bob’s ID, verifies the request, and processes the transfer.
In this analogy:
- Bob’s mobile wallet is the car — it gets him there.
- The bank teller is the dApp interface — receiving the request.
- Bob’s ID and signature is cryptographic verification.
- The entire trip is the manual method — time-consuming and error-prone.
Now imagine this instead:
Bob stays home. His bank app talks directly to his wallet app, asking for permission to transfer $500 to Alice. Bob gets a one-tap confirmation: “Do you approve this?” He taps yes. Done.
That’s the A2A protocol in practice — applications talking to each other so that Bob doesn’t have to make the trip.
Core Components of the A2A Protocol
At its heart, the A2A protocol is built on several key components:
1. Request/Response Model
// dApp sends a connection request to the user's wallet
const connectionRequest = {
type: "connect",
payload: {
appName: "MyDApp",
appUrl: "https://mydapp.io",
timestamp: Date.now()
}
};
// Wallet responds after user approval
const connectionResponse = {
type: "connect_response",
payload: {
approved: true,
walletAddress: "0x1234...abcd",
sessionId: "sess_7890",
timestamp: Date.now()
}
};2. Secure Identity & Authorization
All requests and responses are cryptographically signed using the user’s private key stored in the wallet. This ensures:
- Authenticity (it really came from the wallet)
- Integrity (data hasn’t been tampered with)
- Non-repudiation (it can’t be denied later)
3. Transport Layer
The communication can happen over:
- Deep links
- QR codes (for web-to-mobile)
- Bridge servers (e.g., WalletConnect)
- Bluetooth, NFC, or even encrypted sockets in some cases
4. Session Management
A session is a temporary, secure connection between two apps.
// Creating a new session
const session = {
sessionId: generateSessionId(),
walletAddress: "0x1234...abcd",
expiresAt: Date.now() + 10 * 60 * 1000 // 10 minutes
};
// Terminate session
function terminateSession(sessionId: string) {
sessionStore.remove(sessionId);
console.log("Session ended:", sessionId);
}Sessions are scoped only the actions the user approved are allowed. No hidden permissions.
Technical Deep Dive
Let’s walk through a typical A2A interaction, such as connecting a wallet to a dApp.
Step 1: App initiates connection
const request = {
type: "connect",
payload: {
appName: "DemoSwap",
appUrl: "https://demoswap.io",
requestId: "req-001",
timestamp: Date.now()
}
};This is sent to the wallet, often via a WalletConnect bridge or a deep link.
Step 2: Wallet prompts user for approval
function onReceiveRequest(request) {
if (request.type === "connect") {
showPromptToUser("App DemoSwap wants to connect to your wallet");
}
}Step 3: User approves and wallet responds
const response = {
type: "connect_response",
payload: {
approved: true,
walletAddress: "0xabc...789",
sessionId: "sess_001",
signature: sign(request.payload), // cryptographic signature
timestamp: Date.now()
}
};The sign() function uses the wallet’s private key.
Step 4: Sending a signing request
const signRequest = {
type: "sign",
payload: {
message: "Approve trade of 10 USDC",
sessionId: "sess_001",
nonce: "xyz-123"
}
};
const signature = wallet.sign(signRequest.payload.message);
const signResponse = {
type: "sign_response",
payload: {
signature,
timestamp: Date.now()
}
};Security Considerations
Security is foundational to A2A:
- End-to-End Encryption: Prevents tampering or snooping
- Signature Verification: Ensures authenticity of messages
- Limited Session Scope: Apps can only perform approved actions
- Session Expiry: Reduces attack surface
If Bob approves one signature, he’s not giving the app blanket permission forever.
Real-World Use Cases
The A2A protocol is used in multiple ecosystems:
Web3 Examples
- WalletConnect — Connects mobile wallets to browser-based dApps
- MetaMask Mobile — Uses deep linking for dApp access
- SIWE (Sign-In with Ethereum) — Authenticates users without passwords
Broader Applications
- Healthcare — Apps exchanging health records securely
- IoT — Devices interacting without manual pairing
- Banking — Personal finance apps verifying identity via wallets
Challenges and Limitations
While powerful, A2A protocols still face growing pains:
- Lack of Standardization: Different projects implement it differently
- Session Confusion: Users may not fully understand what’s authorized
- UX Gaps: QR codes and popups can feel clunky without polish
- Bridge Dependence: Many rely on central relays (e.g., WalletConnect bridge servers)
Community-driven specs like CAIP (Chain Agnostic Improvement Proposals) are working to address this.
The Future of A2A
As decentralized identity and zero-knowledge proofs mature, A2A will grow more powerful:
- Sign only if conditions are met
- Authenticate anonymously with ZK
- Chain interactions between apps into a single seamless flow
A2A could become the foundation for autonomous agents, smart wallets, and AI-integrated apps that manage secure interactions on your behalf.
The A2A protocol is more than a communication bridge — it’s a reimagining of how applications trust, verify, and interact. By reducing friction and placing security at the core, A2A helps developers create apps that “just work” without compromising the user experience.
Bob doesn’t need to drive to the bank anymore.
Now, the bank drives to Bob.
Find us
Balian’s Blogs Balian’s
linkedin Shant Khayalian
Facebook Balian’s
X-platform Balian’s
web Balian’s
Youtube Balian’s
#a2a #web3 #protocols #walletconnect #blockchain #decentralization #appdevelopment #crypto #developer #dapps #digitalidentity #interoperability